Blog
BrainStorm Blog
Digital employee experience: Bridge the gap between HR & IT
Learn how to bridge the divide between HR and IT to enhance the digital employee experience and deliver long-term ...

Data — why IT + HR are failing, and how to fix it.
You’re tired.

5 things every IT person must do for threat defense.
It’s hot outside.
Stop the software blues: how to fix the top 3 IT challenges
According to McKinsey, change now happens 10x faster, at 300x the scale, and 3,000x the impact, as it did during the ...
How to fight the 7 sins of software adoption
Software adoption can be hard. Learning new things is always hard. Who didn’t end up with a skinned knee or two while ...

5 learning strategies to get your team up to speed in 1/2 the time
When it comes to training—for new tech, security, HR, customer service, or other purposes—sharing the information with ...

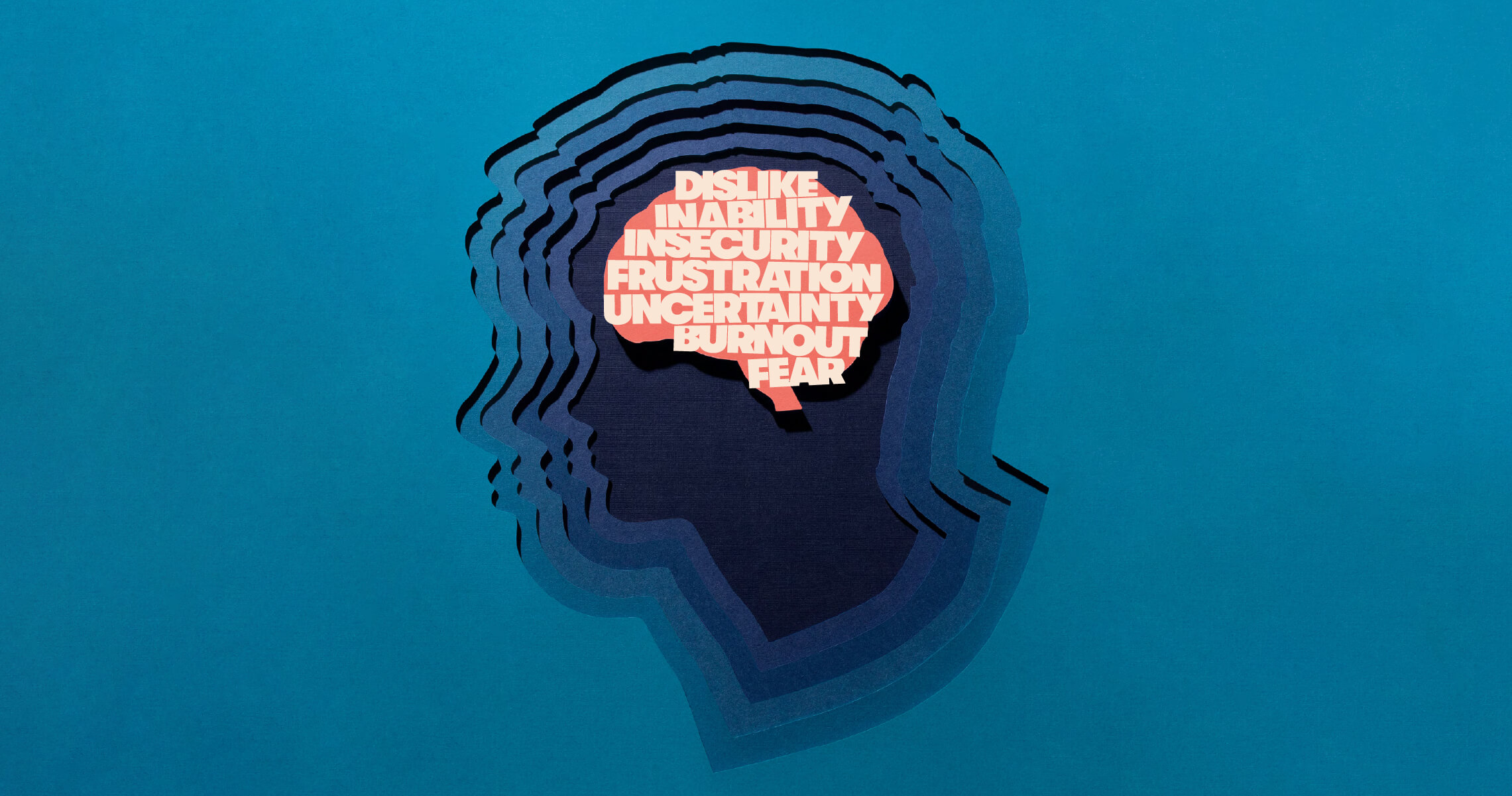
How to improve employee cybersecurity awareness—without shame or fear
As a security leader, you understand the need for cybersecurity awareness training. When it comes to security, the best ...
Cybersecurity risk management: A resource roundup
You want to teach your users about cybersecurity and phishing, and you want the training to stick. There are many ...

Data compliance and the 6 types of CISOs
Think about all the data your organization generates, uses, and stores. Things like customer contact information, ...
.jpg)
The digital employee experience and cybersecurity: What the data say
These days, most organizations are striving for an improved digital employee experience. But what about the ...